All articles containing the tag [
Key Management
]-
Practical Experience And Precautions In Building A Hybrid Cloud Architecture Using Us Cn2 Cloud
practical experience and detailed operation guide for building a hybrid cloud architecture based on the us cn2 line cloud environment, including network design, vpn/dedicated line configuration, routing/nat, storage and synchronization, testing and troubleshooting, and security precautions.
cn2 cloud hybrid cloud hybrid cloud architecture vpn bgp vpc data synchronization network optimization security reinforcement -
Malaysia Vps Server Security Reinforcement And Protection Practical Operation Guide
for vps deployed in malaysia, it provides practical security guides from initial hardening, ssh and firewall settings, patch and permission management, to ddos protection, backup and log monitoring.
malaysia vps vps security server reinforcement ssh security firewall ddos protection backup and recovery log monitoring -
Compliance And Data Protection Regulations And Compliance Advice For Japan Taiwan Cloud Server Cloud Hosting
for enterprises deploying cloud services in japan and taiwan, this article outlines applicable regulations, cross-border transmission risks, technical and contractual compliance points, as well as practical suggestions on how to select cloud vendors and implement data protection measures.
japanese cloud server taiwan cloud host compliance data protection personal information protection law cross-border transfer cloud host regulations -
How Enterprises Evaluate The Security And Compliance Of Cloud Server Hosting Solutions In Malaysia
a practical guide for enterprises: how to evaluate <b>the security</b> and <b>compliance</b> of cloud server hosting solutions in malaysia, including risk assessment, compliance checklist, practical testing and scoring model for selecting suppliers, in line with google eeat standards.
malaysia cloud server hosting cloud security compliance pdpa iso27001 soc2 data sovereignty -
Taiwan Live Broadcast Server Ranking List Security Analysis Protection And Ddos Response Capability Assessment
detailed evaluation of the security, ddos protection and response capabilities of taiwan's live broadcast servers, comparing the best, best and cheapest options, covering network layer, application layer protection, monitoring, backup and sla recommendations to help select the most suitable taiwan live broadcast server provider.
taiwan live broadcast server live broadcast server ranking ddos protection server security taiwan server evaluation live broadcast bandwidth waf cdn server cost performance -
Advantages Comparison And Provider Selection Guide Of Cloud Server Hosting Services In Malaysia
comprehensive comparison of cloud server hosting services in malaysia, analysis of performance, cost, security and compliance points, and a practical checklist and scoring model for supplier selection to help enterprises deploy high-availability, low-latency cloud infrastructure in malaysia.
malaysia cloud servers cloud server hosting data centers local providers bandwidth and latency security compliance backup and disaster recovery -
Security Article Teaches You How To Protect Private Keys And Transaction Security In Singapore Vps Bitcoin Payment
detailed review: how to protect private keys and ensure transaction security when using bitcoin payments on a singapore vps. includes best practices, cost/performance trade-offs, offline signing and backup recovery strategies for users looking for the best and cheapest solution.
singapore vps bitcoin payment private key protection transaction security vps security server encryption -
Practical Tutorial: U.s. Server Code Encyclopedia, Tables And Diagrams Combined With Scripts To Achieve Automated Management
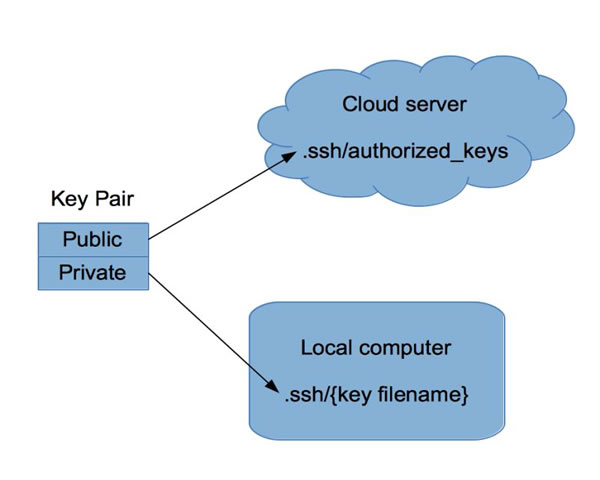
a practical tutorial based on american servers, providing code encyclopedia, tables and diagrams, combined with scripts to achieve automated management, covering deployment, backup, monitoring and security.
american server automated management scripts code collection charts ssh ansible docker -
Discussing Japanese Ss Server Address Password Management And Encryption Practices From A Network Security Perspective
from a network security perspective, analyze the best practices and risk management of ss servers deployed in japan in terms of address management, password and key life cycle, and encryption practices.
japanese ss server address management password management encryption practice network security shadowsocks aead